Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124

Extensions of browsers can be a great way to increase productivity during viewing. Chrome, which is the most popular browser outside, supports a wide range of extensions, including other chromium -based browsers. However, these extensions are not always useful. Although many are useful to block ads, find the best offers or check grammar errors, some may eventually do more damage than benefits.
Recently alone reported on a group of malicious extensions What are the theft of user data, and now the new report has been indicated by another 35 suspicious. These browser extensions require unnecessary licenses and are reported to collect and share everything you do online.
Join the free “Cyberguy Report”:: Get my professional technological advice, critical security warnings and exclusive offers, plus your current approach to my freely “Ultimate Survival guide to fraud “ When you log in!

The man using the Google Chrome browser on his laptop. (Kurt “Cyberguy” Knutsson)
Recent Investigation by John TucnerThe founder of Secure Anex, revealed concerns about 35 chrome extensions, presenting potential privacy and security risks. These extensions, many not listed in the Chrome web store, have been collectively installed more than 4 million times.
Many of these sketched extensions have presented themselves as a search tools in search of searching, blocking ads, monitoring safety or expansion scanning, but have shared a relationship with one, unused domain, suggesting coordinated behavior. They all use the same forms of code, connect with some of the same servers and require the same list of permits for sensitive systems, including the possibility of interaction with the web traffic on all the URL visited, access to cookies, browser cards and scripts.
What is more about the fact that at least 10 of these extensions wore Google’s “prominent” badge, which implies reliability check. This raises questions about Google’s review process, as the badge suggests respecting high standards for user experience, privacy and security.
Hacker at work. (Kurt “Cyberguy” Knutsson)
How to stay incognito and cover up your number when you call someone
The main concern is the level of approaches that quietly seek and how they use them. In addition to reading cards, access to cookies, intercepting web requests and injection of scripts on pages, they can monitor almost everything you do in your browser. This includes monitoring review activities, observing the sign -in sessions and changing the content of the websites you visit, all without your knowledge.
These extensions are not only misunderstood tools. They appear to be deliberately designed with respect to supervision. Many store their configuration information locally, allowing remote servers to update their behavior at any time. This setting is usually seen in spy software, where changes can be made after installation without user warning. The code is very forbidden, making it difficult for researchers to understand what they are actually doing.
In some cases, the extensions do not seem to do anything at all when they click. However, they continue to send data in the background. For example, the protection against the expansion of the fire shield remained inactive until the researcher manually launched it with a certain extension ID. Only then did he begin to transmit review activity and other information, discovering behavior that would be difficult for average user to detect.

The person working on his laptop. (Kurt “Cyberguy” Knutsson)
Malicious software exposes 3.9 billion passwords in a huge cyber -safety threat
35 extensions cannot be searched publicly at the Chrome web store, which means that they can only be installed through direct URL. A complete list of extensions is:
If you have installed one of the extensions above to your browser, remove it as soon as possible. To remove the extension from Google Chrome on the desktop, follow these steps:
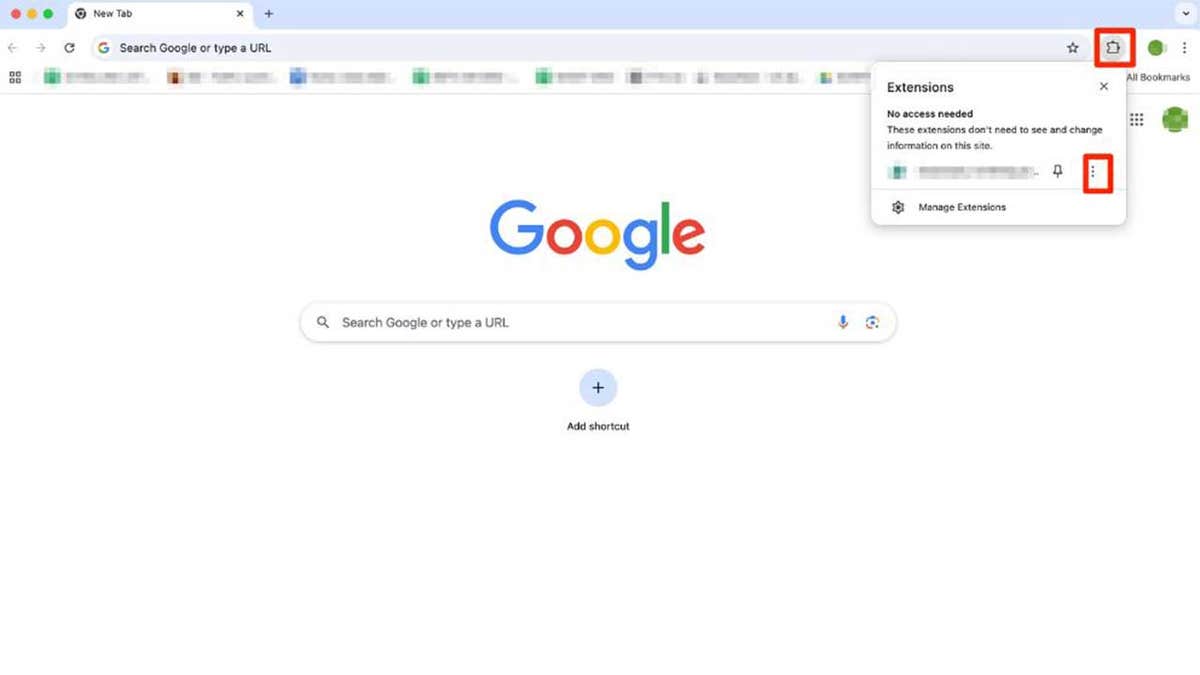
Steps to remove extension from Google Chrome. (Kurt “Cyberguy” Knutsson)
How to remove your private information from the Internet
If you take care of the above extensions, here are five ways to protect your sensitive data and maintain your internet privacy.
1) Keep the browser in progress: Chrome gets regular updates that get rid of most security problems. Be sure to include automatic updates for your browser (eg Chrome, Firefox, Edge), so you always start the latest version without thinking about it. Look at my guide on Update your devices and apps For more information.
2) Install extensions only from reliable sources: Official browser stores like Chrome Web Store have rules and scanning to catch bad actors. They are not perfect, but they are still a better option compared to accidental websites on the Internet. Expands from unknown websites or third -party downloads are far more likely to hide the malicious software or spy software.
3) have a strong antiviral software: A good antivirus can warn you before installing malicious software, such as sketched browser extensions. You can also warn you of phishing e -mail and ransomware fraud, helping to make your personal information and digital assets safe. Get my best winners to protect against antivirus 2025 for your Windows, Mac, Android and iOS devices.
4) Be suspicious of expansion seeking unnecessary approach: Some extensions deliberately prevail. A calculator tool that seeks your viewing history or a time app that wants your application information is a huge red flag.
Before installing, ask, “Does this permission be an extension job?” If the answer is no, don’t install it. Beware of wide permissions such as “Read and change all your information on the website you visit” unless it is clearly justified (eg, password manager). If the update suddenly adds new permission requirements, dig up why. This may mean that the extension has been sold or hacked.
5) Change the passwords and do it safely: If you have ever saved the passwords in your browser (eg, through the built-in Chrome-built password manager or accelerate the “Save password”), and the credentials could be at risk if the malicious extension is installed. These built -in managers store passwords locally or your Google, Microsoft or Firefox account, and a compromised browser can give bad actors a way.
This is usually not related to the dedicated extensions of the password manager, which independently encrypt your data and do not rely on browser storage. However, if you are not sure if the expansion is threatened, it is always wise to update your home password and enable a two -factor authentication.
For maximum safety, change your most important passwords (E -stio, bank, shopping, cloud services) from another, safe device, such as your phone or other computer, where a questionable extension has never been installed. Avoid using the same browser that may have been exposed. Then consider switching to a password manager to create and store powerful, unique applications that go ahead. I examined the main options in my Best password leaders from 2025.. See which best fit into your needs.
The fact that several of these extensions wore Google’s “prominent” badge should serve as an awakening call. This indicates a serious bypass and causes concern about how thorough the Chrome examination is actually. When millions of users unconsciously install spy software under the impression that it was checked and approved, the problem no longer applies to bad actors. Reflects a deeper failure within the platform itself. Google must take over the stronger responsibility by improveing transparency and tighten your viewing standards.
Do you think browser manufacturers like Google should be more responsible for what is published in their stores? Let us know by writing us on Cyberguy.com/contact
For more of my technological tips and security warnings, subscribe to my free newsletter about Cyberguy Report, moving toward Cyberguy.com/newslettter
Ask the Kurt question or let us know which stories would you like to cover.
Follow Kurt on his social channels:
Answer to the most demanding questions about Cyberguy:
New from Kurt:
Copyright 2025 Cyberguy.com. All rights reserved.