Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Phrying attacks are everywhere, and most of us can notice the obvious. Even if one falls into one and hand over the password, a dual -factor authentication (2FA) is usually adding a key layer of protection. However, a new identity stealing set that makes a round can fully bypass the 2FA using the abduction of the session and credentials in real time.
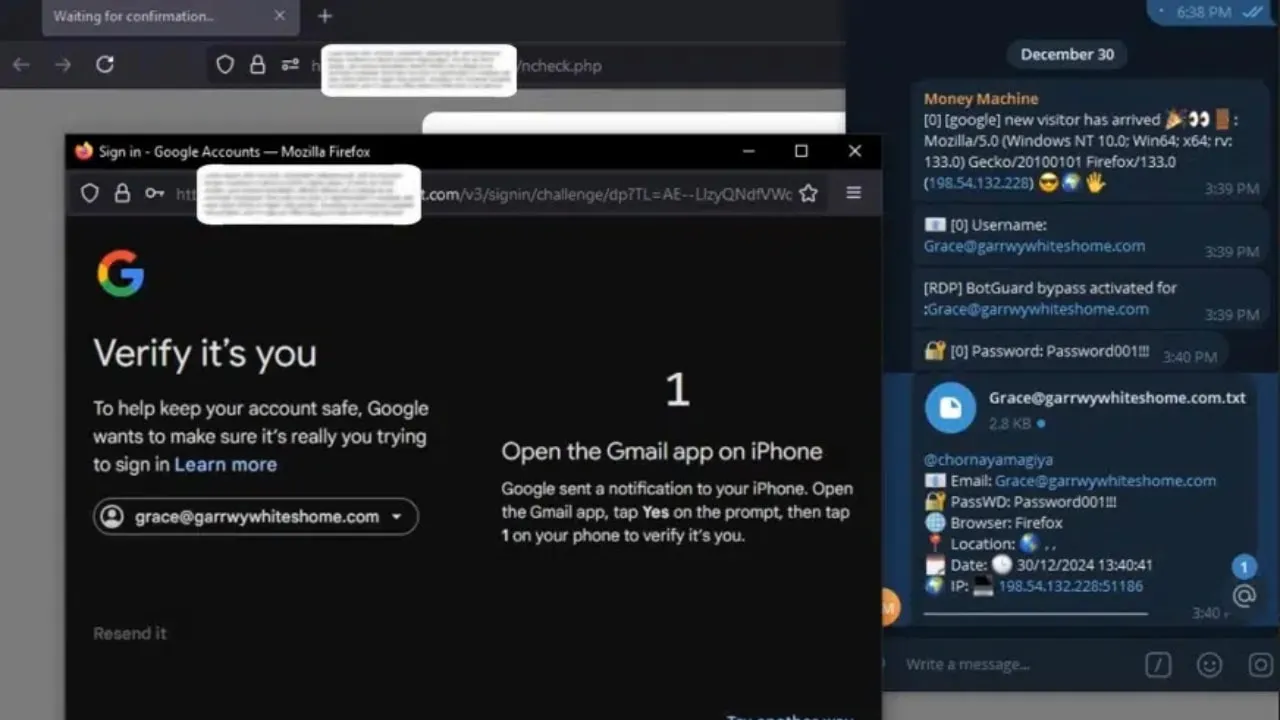
Known as Astaroth, this tool intercepts and manipulates traffic between your device and legitimate authentication services such as Gmail, Yahoo and Microsoft. Since she grabs everything in real time, he completely bypasses the 1F and allows the attackers to access your account full.

Hacker illustration (Kurt “Cyberguy” Knutsson)
Astaroth is a set for the stealing of the next level identity that frauds to a brand new level. Instead of using the basic false application pages such as traditional identity stealing kits, it acts as an intermediary between your device and the true authentication services, while quietly grabs everything it takes to break through.
The attack begins when you click on the stealing relationship and land in a malicious place that looks identical to the right. Since the web site has valid SSL certificates, no red flags, no security warnings and no tickling jump windows. When you enter your application information, including the username, password, device information and IP address, Astaroth installs them before transferring the request to the actual website.
Authentication with a two -factor Not a problem for Astaroth. The one -time password intercepts the other entered, whether they come from the authenticator, SMS or push notification application. The stolen codes are immediately sent to the attacker via the web board or the Telegram warnings so that they can use them before expiration.
The real striker is that Astaroth also grabs the session cookies, which are small bits of data that keep users reported after authentication check. The attackers can inject these cookies into their browsers, completely skipping the need for password or dual -factoric authentication. Once they maintain the session, they are in some additional step.
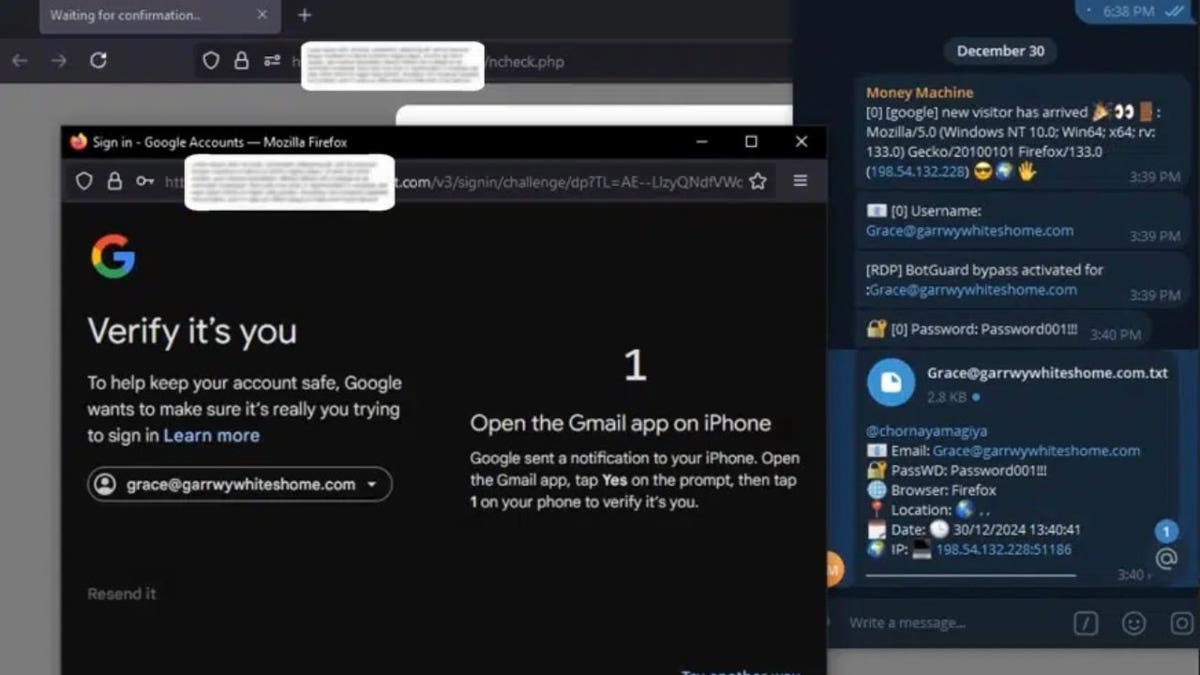
Example of what the victim and the attacker would see (Slashnext) (Kurt “Cyberguy” Knutsson)
Best Antivirus for Mac, PC, iPhone and Androids – Cyberguy Picks
As reported by Cyber -Safe HairAstaroth stands out from other identity stealing kits because of its ability to intercept the real -time credentials, automation of attacks and resisting efforts in removal. Traditionally theft of identity depends on the deceiving victim to enter their credentials on false application pages, but Astaroth completely removes that step.
In addition to its advanced capabilities, Astaroth comes with features that make it attractive cyber -criminals. He uses impenetrable hosting to stay online, despite the efforts to implement the law, receives frequent updates to bypass security patches and follow the structured payment model. For $ 2,000, customers get six months of continuous upgrade. To build confidence, the creatives even let the hackers test the Phishing kit before buying.
Astaroth is widely available through the Telegram and Underground Cyber Crime. The anonymity of these platforms makes it difficult to monitor the distribution.
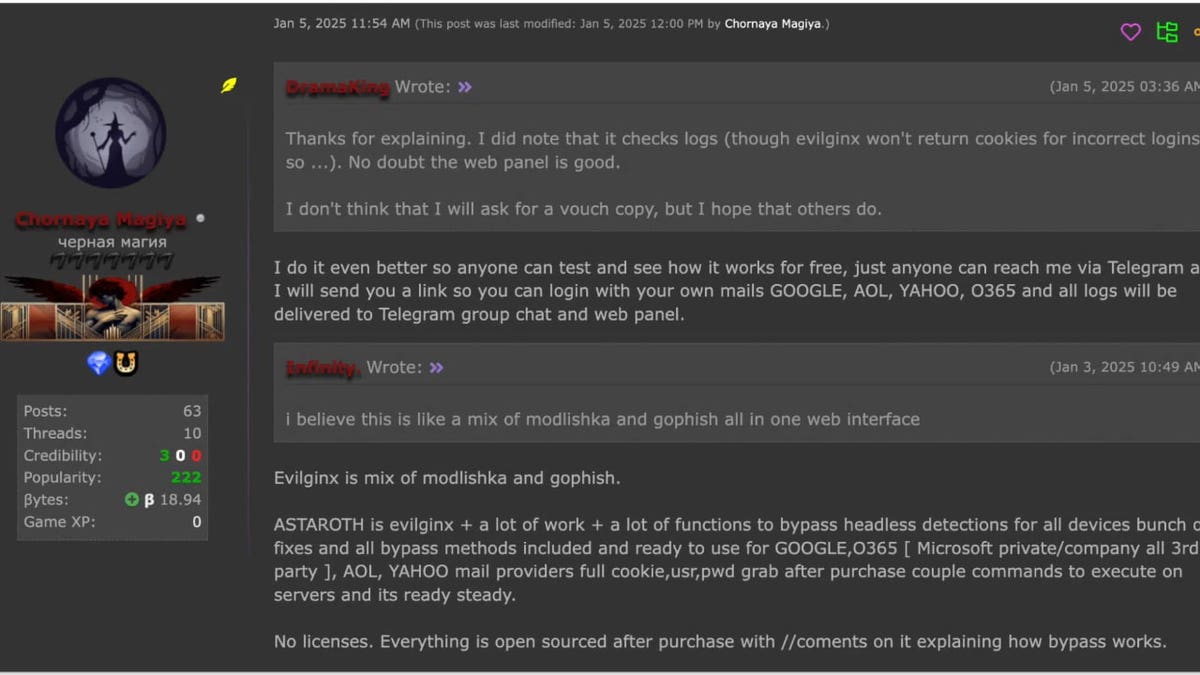
Seller Division Division of Phishing Testing (Slashnext) (Kurt “Cyberguy” Knutsson)
How to protect your information from the IRS fraudster of this tax season
1) Unexpected account applications or security warnings
2) You mysteriously signed up from the account
3) changes or updates of settings you have not made
4) slow performance of the system or unusual behavior
5) A browser that acts unusual
6) unknown programs or scripts that work in the background
1) Avoid unknown connections and use a strong antiviral software: Keep in mind that no matter how advanced the malicious software was advanced, it still needs intake from you. In most cases, the attacker will require you to click the relationship before stealing your data. For example, in order for Astaroth to do, you need to click on a relationship, visit a malicious site and enter your credentials. If you don’t click on the relationship, you stay away from the malicious software.
The best way to protect yourself from malicious connections installed by malicious software, potentially access to your private data, is to install a strong antivirus software on all your devices. This protection can also alert you of phishing e -Mail and fraud from Ransomware, keeping your personal information and digital assets. Get my elections for the best winners to protect against antivirus 2025 for your Windows, Mac, Android and iOS.
2) Websites with double checking: Always check the website addresses and use the labels for reliable websites. Instead of clicking on the UE -MAILS or MESSAGES, Type the URL manually or use a reliable tag. This minimizes the risk of landing on the false page intended to mimic a legitimate website.
3) Update your devices: You can wonder how to update your device helps with malicious software like Astaroth. Although this does not prevent it directly, it ensures that the situation does not worsen. Maintaining your operating system and app updated With the latest security patch, it closes vulnerability that the malicious software could use, which makes it difficult for attackers to fix on your device.
4) Avoid typing passwords: Avoid entering passwords whenever possible to reduce the risk of the stealing credentials. Instead, use authentication methods such as Passkeys, Google Login or Apple Application.
AND KUKEY is a feature that uses pairs of cryptographic keys to check your identity, eliminating the need for traditional passwords. Allows you to log in to apps and websites using the same procedure you use to unlock the device, such as biometry, PIN or sample.
Google Login The feature is that allows you to log in to the app or the third party website using their Google Account credentials. It simplifies the application procedure by removing the need to create and remember separate user names and passwords for each service. You can log in through the “Logom with Google” buttons, Google inquiries for logging or automatically logging if approved previously approved.
Apple is a feature that allows you to register privately to participate in third-party apps and websites using your Apple ID. Offers a quick, simple and more private way to authenticate without the need to create new accounts or remember additional passwords. To set an account to “Log in with Apple”, when a website or application to participate is asking you to set or upgrade the account, do the following: Log in with Apple. Follow instructions on the screen. Some applications (and websites) do not seek their name and address e -Ad. In this case, you are simply authenticated by the ID or Touch ID (depending on your model) and then start using the application. Others may seek your name and address E -stio to set up a personalized account. When the app requests this information, sign up with Apple shows your name and personal address E -Ap from your Apple account for review.
These methods rely on cryptographic keys or safe tokens, which significantly makes it difficult for attackers to intercept your application information, even if you are able to deceive you in a visit by a malicious place.
FBI warns of a dangerous new fraud ‘meaning’ which targets your phone
Astaroth shows how many distant phishing kits came, getting things beyond the usual tricks is easily bypassing the 2Fa. The reminder is that no matter how sure we are, our systems always have a smarter attack that awaits to use emptiness. Cyber-Kriminalians are quickly adjusted, and although traditional defense may not reduce anymore, you can still take steps to fight: use a password without password, stay updated and continue learning about these evolutionary threats.
What do you think government and businesses should do to protect you from sophisticated cyber threats like Astaroth Phishing Kit, which can bypass traditional security measures? Let us know by writing us on Cyberguy.com/contact.
For more of my technological tips and security warnings, subscribe to my free newsletter about Cyberguy Report, moving toward Cyberguy.com/newslettter.
Ask the Kurt question or let us know which stories would you like to cover.
Follow Kurt on his social channels:
Answer to the most demanding questions about Cyberguy:
New from Kurt:
Copyright 2025 Cyberguy.com. All rights reserved.